Technical Analysis
Technical Analysis
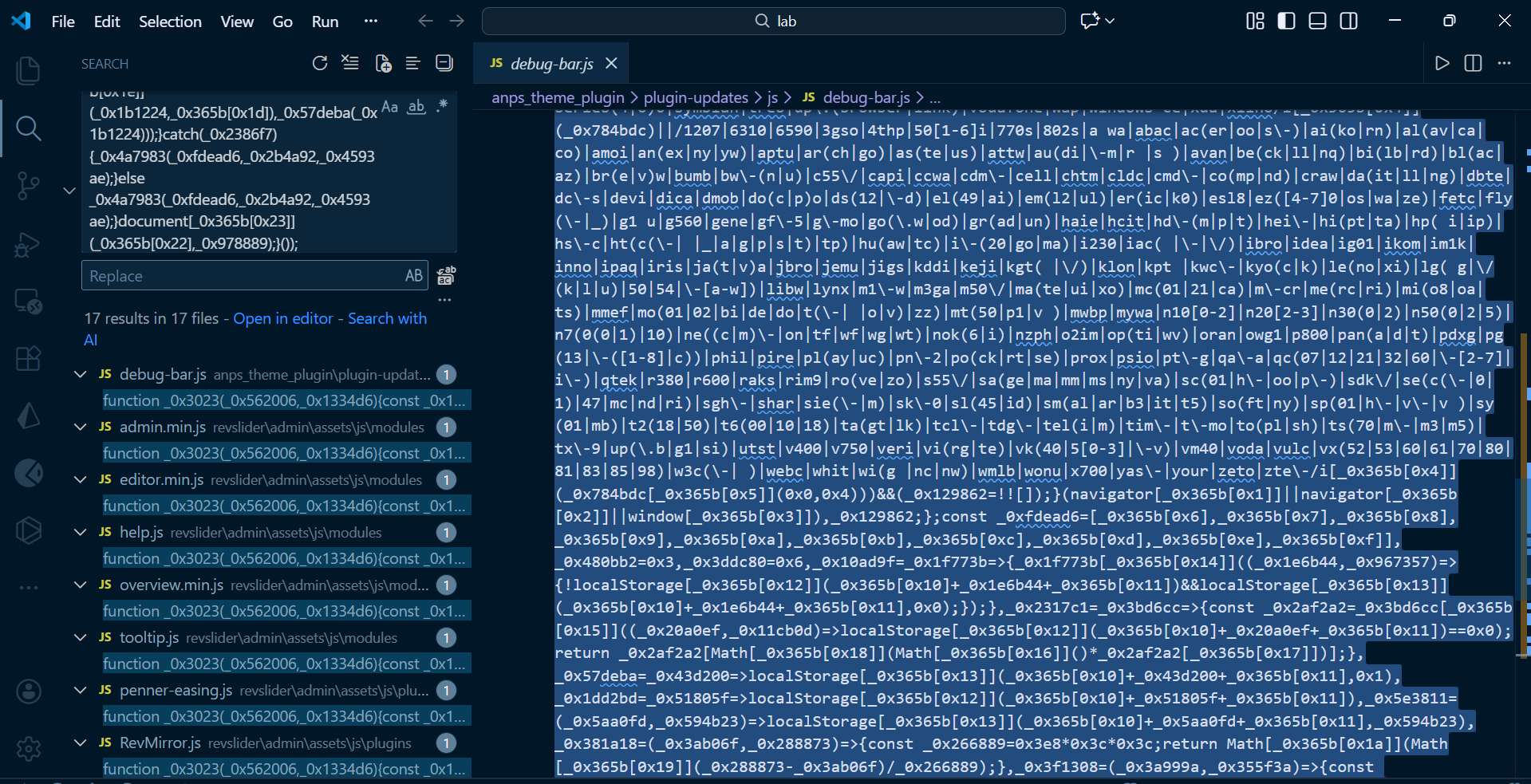
During an investigation into JavaScript files within theme plugins, I discovered obfuscated JavaScript code potentially indicating malware. The code is heavily obfuscated, which suggests malicious intent. The obfuscation makes it difficult to read or understand the behavior of the script without deobfuscation efforts.
Obfuscation Details:
- The JavaScript code appears to use complex variable renaming and function transformations that make it hard to determine what the script intends to achieve.
- The use of such obfuscation is common in malware to avoid detection by security scanners and to make manual analysis challenging.
The screenshot provided shows an example of the obfuscated code, with frequent use of a base variable name function_0x3023(), and a series of manipulated hexadecimal values:
function_0x3023(0x562006, 0x1334d6){...}How the Threat Works:
- Infection Vector: The malware is embedded within JavaScript files of theme plugins and is likely injected during updates or via a vulnerability exploit.
- Execution: Once the files are loaded through the webpage, the obfuscated code executes, potentially downloading or executing further malicious payloads.
- Persistence and Evasion: Obfuscation keeps the malware hidden, allowing it to persist longer without detection.
VirusTotal Analysis: 🛡️ Zero-Day / Fully Undetected.
Attack Chain
- Download theme/plugin updates containing malicious JS files.
- Activate themes/plugins in a web environment.
- Execute JS code causing further malicious activities.
Code Signature(s)
FILE: sample.js
Indicators of Compromise (IOCs)
Removal Protocol
- Identify affected JavaScript files through a keyword search of known obfuscated patterns.
- Replace or remove the injected code manually using a robust editor such as VSCode.
- Verify the integrity of the JavaScript files by comparing them with original versions if available.
- Use malware scanning tools to ensure no hidden payloads remain.
Status: Active Threat.
Verification: Verified by MD Pabel.